Niels Tanis
Securing your application software supply-chain
#1about 3 minutes
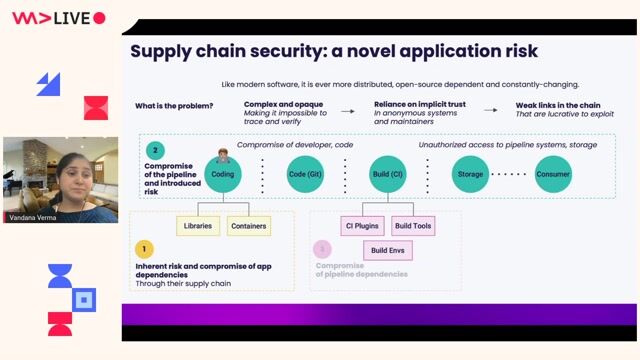
Defining the modern software supply chain
The modern software supply chain encompasses all steps from source code to deployment, growing in complexity with cloud-native development.
#2about 1 minute
Learning from the SolarWinds supply chain attack
The SolarWinds incident serves as a key example of a supply chain attack where a compromised build server injected malicious code into a signed product.
#3about 3 minutes
Securing developer access and development tools
Protect source code access by implementing multi-factor authentication and git commit signing, while also considering the security risks within your IDE's own supply chain.
#4about 5 minutes
Managing risks from third-party libraries
Mitigate risks from third-party dependencies by addressing vulnerabilities, preventing dependency confusion, and using tools like OpenSSF Security Scorecards to assess package health.
#5about 3 minutes
Ensuring integrity with reproducible builds and signing
Create verifiable software by implementing reproducible builds and using tools like Sigstore and Cosine for keyless signing of artifacts like Docker images.
#6about 4 minutes
Creating a software bill of materials (SBOM)
A Software Bill of Materials (SBOM) acts like a parts list for your software, enabling you to track all components using tools like CycloneDX and Syft.
#7about 3 minutes
Adopting the SLSA framework for supply chain maturity
The SLSA framework provides a maturity model with incremental levels to help organizations progressively secure their software supply chain.
#8about 2 minutes
Implementing and enforcing supply chain policies
Apply supply chain security in practice with validation pipelines like SolarWinds' Project Trebuchet and enforce policies using tools like Kyverno and Google's Binary Authorization.
#9about 3 minutes
Key takeaways and next steps for securing your supply chain
The key to securing your supply chain is to be aware of its complexity, integrate security from the start, and begin by generating and eventually ingesting SBOM data.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
01:31 MIN
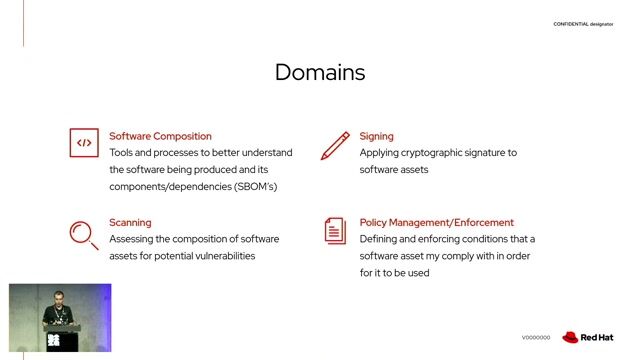
Exploring the core domains of supply chain security
Open Source Secure Software Supply Chain in action
Unlock full access
Log in or set up an account to access this feature and more.
04:45 MIN
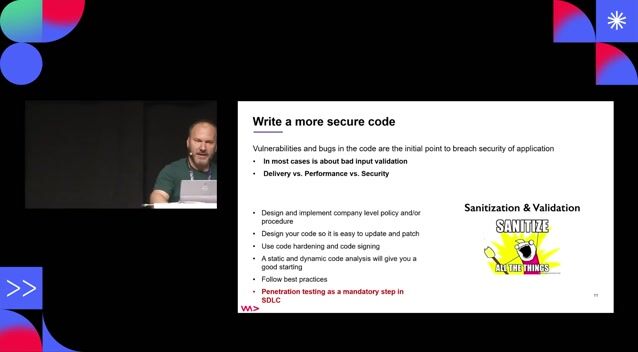
Mitigating supply chain attacks with DevSecOps practices
Security Pitfalls for Software Engineers
Unlock full access
Log in or set up an account to access this feature and more.

01:46 MIN
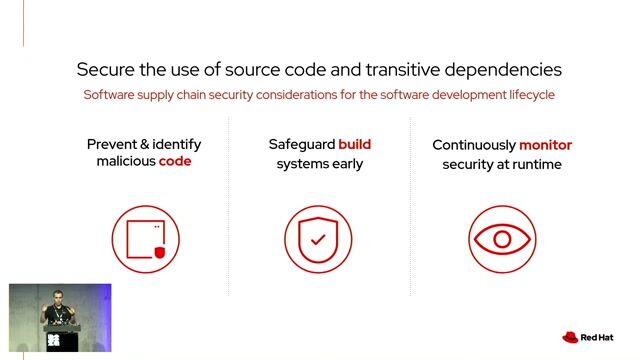
Understanding the rising threat to software supply chains
Open Source Secure Software Supply Chain in action
Unlock full access
Log in or set up an account to access this feature and more.

02:21 MIN
Defining key standards and terminology in supply chain security
Open Source Secure Software Supply Chain in action
Unlock full access
Log in or set up an account to access this feature and more.
04:51 MIN
Using open source tools to secure the entire SDLC
Open Source Secure Software Supply Chain in action
Unlock full access
Log in or set up an account to access this feature and more.
03:32 MIN
Defining the modern software supply chain
Walking into the era of Supply Chain Risks
Unlock full access
Log in or set up an account to access this feature and more.
03:50 MIN
Building a foundation for pipeline security
Walking into the era of Supply Chain Risks
Unlock full access
Log in or set up an account to access this feature and more.
01:52 MIN
Securing container images and the software supply chain
Security Challenges of Breaking A Monolith
Unlock full access
Log in or set up an account to access this feature and more.
Featured Partners
Related Videos
 32:55
32:55Open Source Secure Software Supply Chain in action
Natale Vinto
 26:41
26:41Overcome your trust issues! In a world of fake data, Data Provenance FTW
Jon Geater
 16:00
16:00DevSecOps culture
Ali Yazdani
 51:41
51:41Climate vs. Weather: How Do We Sustainably Make Software More Secure?
Panel Discussion
 26:50
26:50Organizational Change Through The Power Of Why - DevSecOps Enablement
Nazneen Rupawalla
 24:47
24:47Supply Chain Security and the Real World: Lessons From Incidents
Adrian Mouat
 25:48
25:48Reviewing 3rd party library security easily using OpenSSF Scorecard
Niels Tanis
 37:36
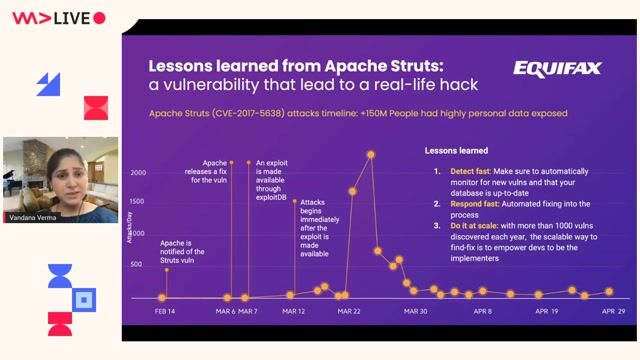
37:36Walking into the era of Supply Chain Risks
Vandana Verma
Related Articles
View all articles.gif?w=240&auto=compress,format)


.png?w=240&auto=compress,format)
From learning to earning
Jobs that call for the skills explored in this talk.


NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

NTT DATA Deutschland GmbH
Remote
Node.js
Continuous Integration

Codasip
Berlin, Germany



