Marc Nimmerrichter
Kubernetes Security - Challenge and Opportunity
#1about 3 minutes
A high-level overview of Kubernetes architecture
The core components of a Kubernetes cluster are explained, including the master node, worker nodes, etcd, API server, and kubelet.
#2about 3 minutes
Configuring workloads with Kubernetes objects
Key Kubernetes objects like pods, deployments, services, and volumes are introduced as the building blocks for configuring applications.
#3about 4 minutes
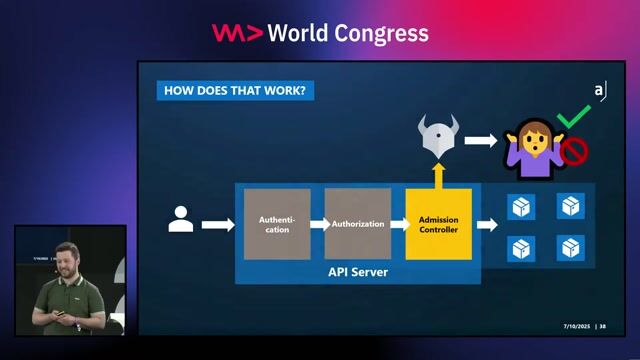
Managing access with namespaces and admission control
Namespaces are used to group resources, while authentication, authorization, and admission controllers provide granular access control through the API server.
#4about 7 minutes
How container isolation works in the Linux kernel
Containers achieve isolation using Linux kernel features like namespaces and cgroups, but share the host kernel, creating a different security model than VMs.
#5about 2 minutes
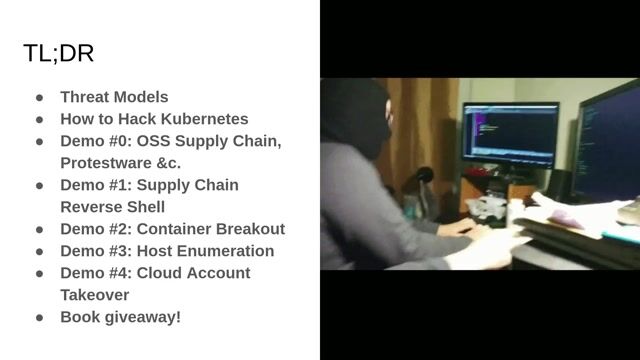
Deconstructing a typical Kubernetes cluster attack chain
An attacker can chain exploits, starting from an application vulnerability and escalating to a full container escape and cluster compromise.
#6about 4 minutes
Identifying common Kubernetes security vulnerabilities
Misconfigurations like privileged containers, disabled namespaces, and unpatched software in runtimes like runc create significant security risks.
#7about 6 minutes
Demonstrating a container escape via kernel exploit
A live demo shows how a kernel vulnerability like Dirty COW can be exploited to escape container isolation and gain root access on the host node.
#8about 4 minutes
The risks of RBAC and essential hardening measures
The `create pod` privilege is dangerously powerful, and security can be improved by enabling hardening measures like seccomp profiles and Pod Security Admission.
#9about 4 minutes
Addressing networking and multi-tenancy security challenges
Kubernetes network policies are essential for segmenting traffic, while true multi-tenancy is extremely risky and requires advanced solutions like hardened runtimes.
#10about 1 minute
Leveraging containerization for improved security posture
Despite the risks, containerization offers security advantages through small, understandable workloads that allow for tight security profiles and automated scanning.
#11about 3 minutes
Q&A on managed Kubernetes security in the cloud
The shared responsibility model in cloud Kubernetes services is discussed, highlighting that users must still explicitly enable many hardening features.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments

01:27 MIN
The prevalence and impact of Kubernetes security incidents
Kubernetes Security Best Practices
Unlock full access
Log in or set up an account to access this feature and more.
06:25 MIN
Security best practices for containers and Kubernetes
Microservices: how to get started with Spring Boot and Kubernetes
Unlock full access
Log in or set up an account to access this feature and more.
08:13 MIN
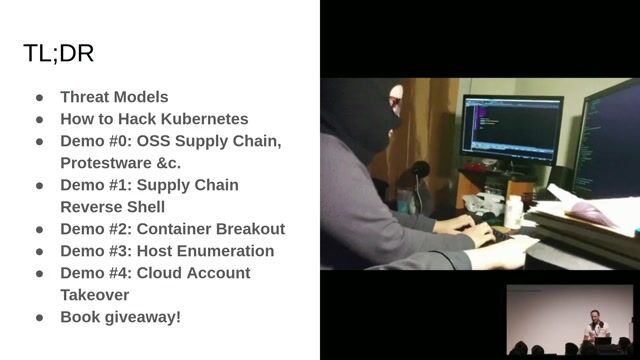
Understanding the Kubernetes threat landscape and adversaries
Hacking Kubernetes: Live Demo Marathon
Unlock full access
Log in or set up an account to access this feature and more.
03:37 MIN
Addressing unique data protection challenges in Kubernetes
It's all about the Data
Unlock full access
Log in or set up an account to access this feature and more.
02:16 MIN
Key takeaways for hardening Kubernetes clusters
Kubernetes Security Best Practices
Unlock full access
Log in or set up an account to access this feature and more.
02:04 MIN
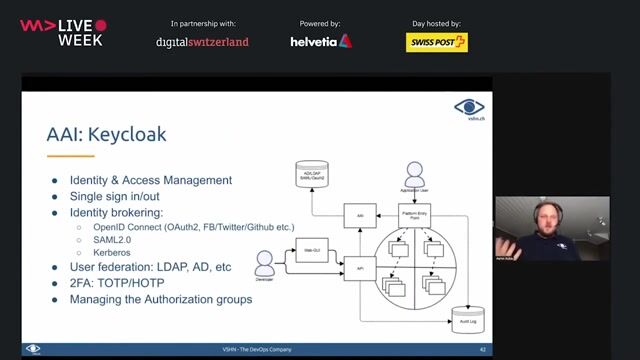
Centralizing security services in a Kubernetes ecosystem
DevSecOps: Security in DevOps
Unlock full access
Log in or set up an account to access this feature and more.

07:59 MIN
Securing containers and infrastructure as code (IAC)
Maturity assessment for technicians or how I learned to love OWASP SAMM
Unlock full access
Log in or set up an account to access this feature and more.
01:52 MIN
Understanding Kubernetes as a foundational platform
Effective Java Strategies and Architectures for Clouds
Unlock full access
Log in or set up an account to access this feature and more.
Featured Partners
Related Videos
 46:36
46:36Hacking Kubernetes: Live Demo Marathon
Andrew Martin
 44:00
44:00Enhancing Workload Security in Kubernetes
Dimitrij Klesev & Andreas Zeissner
 40:00
40:00Local Development Techniques with Kubernetes
Rob Richardson
 28:47
28:47Turning Container security up to 11 with Capabilities
Mathias Tausig
 28:36
28:36What we Learned from Reading 100+ Kubernetes Post-Mortems
Noaa Barki
 23:08
23:08Kubernetes Security Best Practices
Rico Komenda
 57:24
57:24Mastering Kubernetes – Beginner Edition
Hannes Norbert Göring
 27:52
27:52Chaos in Containers - Unleashing Resilience
Maish Saidel-Keesing
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.




SVA System Vertrieb Alexander GmbH
Düsseldorf, Germany
Openshift
Kubernetes

Westnetz GmbH
Linux
Ansible
Kubernetes
Continuous Integration

Westnetz GmbH
Linux
Ansible
Kubernetes
Continuous Integration

Westnetz GmbH
Linux
Ansible
Kubernetes
Continuous Integration

Westnetz GmbH
Linux
Ansible
Kubernetes
Continuous Integration
