Mauro Verderosa
Getting under the skin: The Social Engineering techniques
#1about 7 minutes
The 1978 heist that pioneered social engineering
Stanley Mark Rifkin exploited procedural manuals and used pretexting to steal millions from a bank without any technical hacking.
#2about 3 minutes
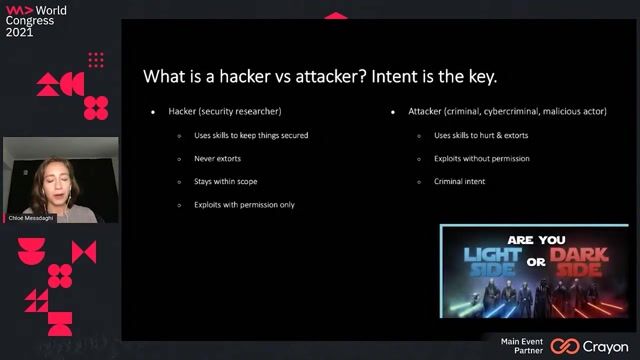
Understanding the five main motivations for cybercrime
Cyber attacks are driven by distinct goals, including financial gain, business competition, political influence, ideology, or simple curiosity.
#3about 5 minutes
What social engineering is and its real-world impact
Social engineering is the psychological manipulation of people to divulge information, as seen in major breaches at companies like RSA and Sony.
#4about 7 minutes
An overview of common social engineering attack techniques
Attackers use various methods like pretexting, phishing, baiting, and tailgating to trick victims into compromising security.
#5about 2 minutes
Psychological triggers that make social engineering effective
Attacks succeed by exploiting human emotions and cognitive biases such as authority, guilt, panic, desire, and greed.
#6about 4 minutes
Deconstructing real-world phishing and vishing attacks
A simple phishing email is analyzed for pressure tactics, followed by a vishing example where an attacker impersonates a spouse to gain account access.
#7about 5 minutes
Understanding the complete social engineering attack lifecycle
A successful attack follows distinct phases, from initial reconnaissance and scanning to lateral movement, data exfiltration, and finally covering tracks.
#8about 6 minutes
A step-by-step case study from Mr. Robot
An elaborate attack demonstrates how gathering small, public details from social media and real-world observation leads to a full account compromise.
#9about 5 minutes
Key takeaways and defenses against social engineering
The most effective defense against social engineering is continuous employee training and fostering a security-aware culture to patch the human vulnerability.
Related jobs
Jobs that call for the skills explored in this talk.
Matching moments
03:11 MIN
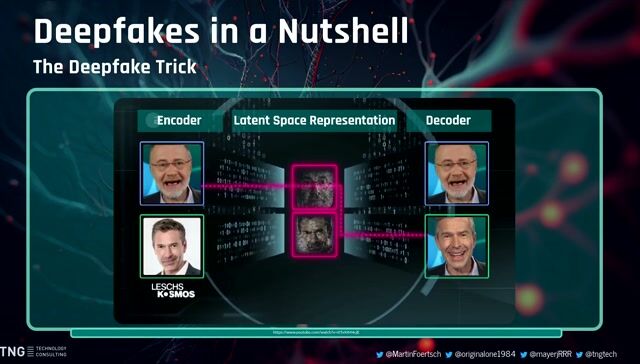
Demonstrating deepfake attacks and social engineering
The AI Elections: How Technology Could Shape Public Sentiment
Unlock full access
Log in or set up an account to access this feature and more.
03:16 MIN
A social engineering attack using a personal email
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock full access
Log in or set up an account to access this feature and more.

27:22 MIN
Q&A on social engineering and a career in security
Stranger Danger: Your Java Attack Surface Just Got Bigger
Unlock full access
Log in or set up an account to access this feature and more.

02:26 MIN
Why developers make basic cybersecurity mistakes
Don't Be A Naive Developer: How To Avoid Basic Cybersecurity Mistakes
Unlock full access
Log in or set up an account to access this feature and more.

05:38 MIN
Why attackers use prompt injection techniques
Manipulating The Machine: Prompt Injections And Counter Measures
Unlock full access
Log in or set up an account to access this feature and more.

04:40 MIN
How attackers use AI to refactor exploits
The AI Security Survival Guide: Practical Advice for Stressed-Out Developers
Unlock full access
Log in or set up an account to access this feature and more.

01:21 MIN
A real-world case of deepfake job interview phishing
Deep Fakes: The Lies We Can’t See
Unlock full access
Log in or set up an account to access this feature and more.

05:31 MIN
From vulnerability researcher to automated security founder
The transformative impact of GenAI for software development and its implications for cybersecurity
Unlock full access
Log in or set up an account to access this feature and more.
Featured Partners
Related Videos
 2:08:06
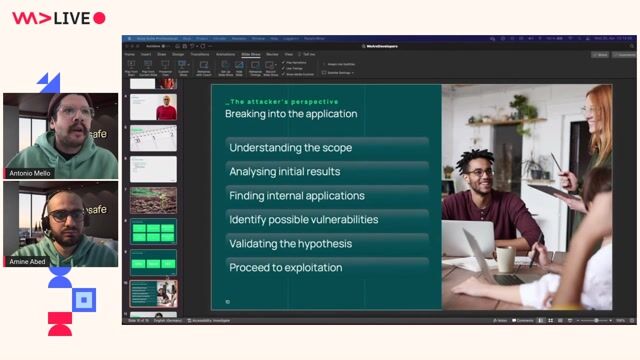
2:08:06The attacker's footprint
Antonio de Mello & Amine Abed
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 29:34
29:34You can’t hack what you can’t see
Reto Kaeser
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
 31:19
31:19Skynet wants your Passwords! The Role of AI in Automating Social Engineering
Wolfgang Ettlinger & Alexander Hurbean
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
 57:47
57:47Cracking the Code: Decoding Anti-Bot Systems!
Fabien Vauchelles
 41:32
41:32We Deserve Rights
Chloé Messdaghi
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.



Pflegecampus21 GmbH
Remote
€55-80K
MySQL
DevOps
TypeScript


Rocken AG



Vesterling Consulting GmbH
€70-90K
Software Architecture
